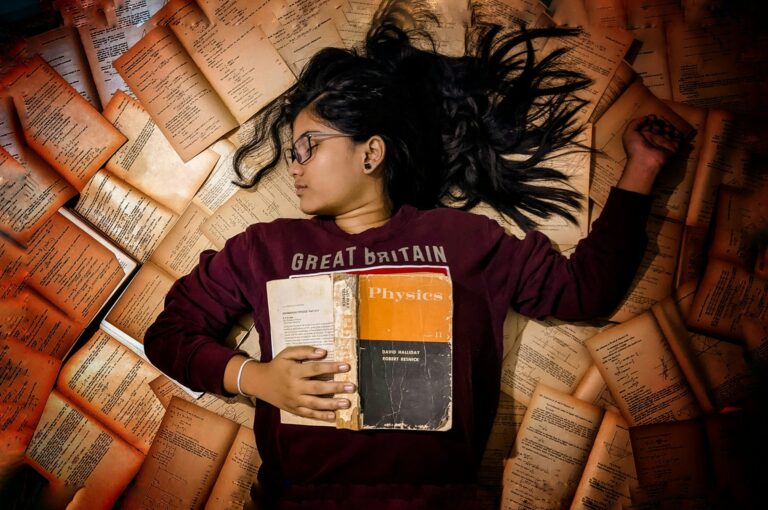
How to Get a Good Grade on Your Semester Exams?
As students, we all strive for academic excellence, and semester exams are a critical measure of our progress. We can enhance our study strategies and improve…
Blogging & Tech Guides
As students, we all strive for academic excellence, and semester exams are a critical measure of our progress. We can enhance our study strategies and improve…
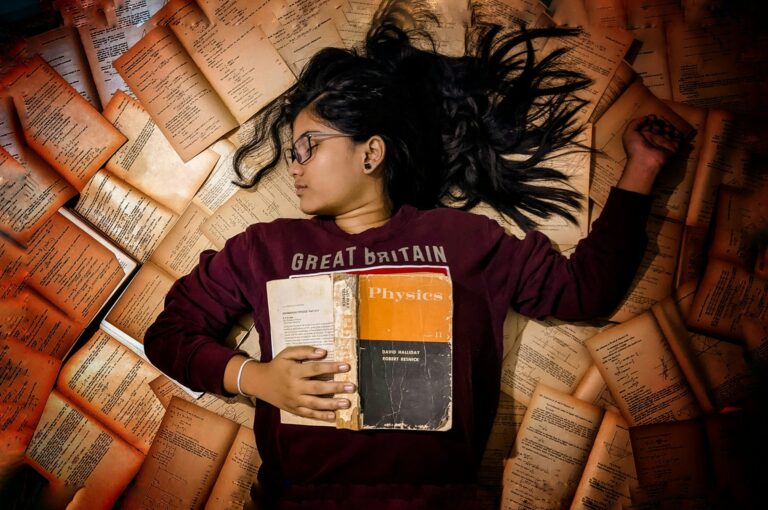
Language models like ChatGPT have appeared as powerful tools. It can generate human-quality text, translating languages, writing different kinds of creative content, and answering your questions…
Blogger outreach is a type of influencer marketing that involves reaching out to bloggers with a loyal audience and asking them to feature your products or…

Blogging is really popular. Nowadays, it seems like everyone has a blog and they are pretty successful too. But how true is that? Approximately, 6 million…

Instagram Direct Messages (DM) are one of the best features of the popular photo-sharing app. While it’s great to receive messages from friends or family, and…

Image via Dreamstime Stock Photos In today’s fast-paced, digitally-oriented society, the way businesses connect with their audiences has drastically changed. Let’s dive into one of the…

Nowadays, Instagram is considered one of the most fantastic social media platforms. This platform has undoubtedly made our lives easier by offering incredible services and high-quality…

The primary source of organic internet traffic is high-quality blog content. No matter how informative or keyword-optimized your text is, you will never be able to…
In the current digital era, bloggers are continuously looking for novel ways to improve their content creation process and better engage their audience. Here, artificial intelligence’s…